
- Self-hosted chat for government means deploying a messaging platform on infrastructure you own and control, with no data leaving your jurisdiction.
- Consumer and cloud-first platforms (Teams, Slack, WhatsApp) do not meet the sovereignty, compliance, or air-gap requirements of most government and defense environments.
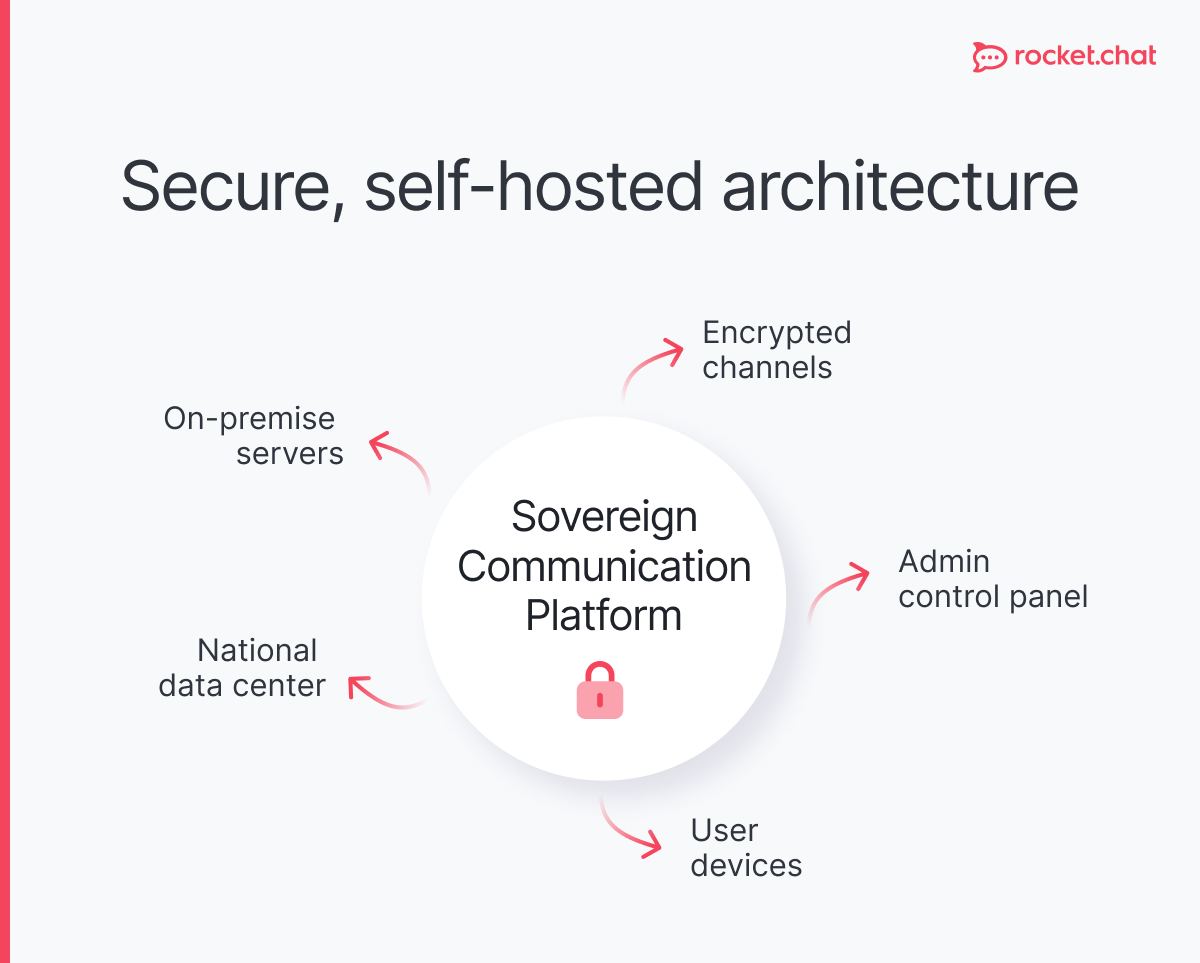
- The minimum viable architecture for a self-hosted government chat platform includes end-to-end encryption, role-based access control, audit logging, and the option for full network isolation.
- Open-source platforms offer the only realistic path to code auditability and long-term vendor independence.
- European governments face additional pressure from NIS2, GDPR, and digital sovereignty directives that make U.S.-hosted SaaS legally problematic.
- Deployment decisions should be made jointly by IT security leads, legal/compliance teams, and operational commanders or senior administrators.
The answer: government agencies need self-hosted chat infrastructure they control entirely
Government agencies that rely on third-party cloud messaging services surrender operational control at the moment it matters most. When a vendor suffers an outage, changes their data residency policy, or receives a foreign legal order, an agency has no recourse. Self-hosted chat for government eliminates that dependency by keeping every message, file, and metadata record on government-owned infrastructure.
This is not a theoretical concern. In 2021, a misconfiguration in a major cloud provider's infrastructure exposed metadata from enterprise customers for several hours before the vendor issued a patch. No self-hosted government chat operator was affected, because they controlled the environment. The architecture decision is the security decision.
Why cloud-based platforms fail government requirements
Most enterprise chat tools were built for corporate productivity, not classified or sensitive government operations. They share three structural problems:
- Data residency is not guaranteed. Cloud providers route traffic across regions for redundancy and performance. Even products that advertise regional hosting often replicate backups or telemetry data outside the contracted geography. For agencies bound by GDPR or national data sovereignty laws, this creates direct legal exposure. Encrypted messaging apps built for government use address this structurally, not as an optional feature.
- Vendor access to encryption keys is the norm, not the exception. Most SaaS platforms encrypt data at rest using keys they manage. That means the vendor, and by extension anyone with legal or extrajudicial access to the vendor's systems, can read your communications. The financial exposure compounds the legal one: public cloud breaches cost $5.17 million on average according to IBM's 2024 Cost of a Data Breach Report — the most expensive storage environment in the study.End-to-end encryption where only the communicating parties hold keys is rare in standard enterprise cloud tools.
- Audit and compliance requirements cannot be met externally. Government agencies must retain records of official communications and provide access for legal discovery or oversight review. When that data sits in a vendor's system, export formats are inconsistent, retention timelines are controlled by the vendor's commercial tier, and chain-of-custody documentation is rarely sufficient for legal proceedings.

What a self-hosted government chat platform actually requires
A self-hosted government chat deployment that meets government-grade requirements is not simply "an on-premise version of Slack." The architecture must address five distinct areas.
- Encryption in transit and at rest, with agency-controlled keys. All communications must be encrypted using current standards (TLS 1.3 for transit, AES-256 for storage). The agency must hold the encryption keys, not the vendor. This is non-negotiable for any on-premise government messaging deployment touching sensitive or classified information. Reviewing the distinction between encrypted messaging and standard messaging makes the operational stakes clear.
- Air-gap capability for the most sensitive environments. Defense and intelligence environments often require networks with no internet connectivity whatsoever. The self-hosted government chat platform must be deployable in a fully air-gapped collaboration environment, with all dependencies bundled and no external calls made at runtime.
- Role-based access control and federation. Large agencies have complex permission structures: field operators, analysts, administrators, and executives all require different access levels. The platform must support granular RBAC and, where multiple agencies or coalition partners collaborate, federated identity management across organizational boundaries.
- Comprehensive audit logging. Every message sent, every file shared, every login attempt, and every administrative action must be logged with tamper-evident records. These logs must be exportable in standard formats and retainable on the agency's own storage systems. Organizational security posture depends heavily on what the audit trail can prove after the fact.
- Open-source codebase. Agencies must be able to inspect, audit, and if necessary modify the source code of any self-hosted government chat platform handling sensitive communications. Proprietary platforms require trusting the vendor's security claims without verification. Open-source communication for government is the only model that allows genuine assurance.
The European regulatory context
European government agencies operate under a converging set of legal requirements that make U.S.-hosted SaaS untenable for most official communications. Three regulatory frameworks are directly relevant to any on-premise government chat decision.
GDPR requires that personal data of EU residents be processed under conditions that guarantee the rights of data subjects. Transfers to third countries without adequate protections have been repeatedly challenged and invalidated. CJEU ruled Privacy Shield invalid, finding that US surveillance programmes are not limited to what is strictly necessary under GDPR, making U.S.-hosted services legally problematic for many government use cases.
GDPR-compliant messaging requires either an EU-hosted deployment or a certified transfer mechanism, neither of which most U.S. SaaS vendors can fully guarantee following the Schrems II ruling.
NIS2 (the Network and Information Security Directive 2) extends mandatory security requirements to a broader set of "essential entities," including many government functions and critical infrastructure operators. NIS2 covers over 160,000 EU entities across 18 sectors — a dramatic expansion from the original NIS Directive — with direct implications for the security standards of any communication platform used by covered entities.
NIS2 compliance has direct implications for the security standards of any communication platform used by covered entities.
Digital sovereignty initiatives across France, Germany, and the EU at large are pushing agencies to assess technology stacks for dependency on non-EU vendors. The GAIA-X initiative and national cloud programs like Germany's Sovereign Cloud reflect a policy consensus that digital sovereignty is a strategic priority, not just a compliance checkbox. Agencies evaluating Microsoft Teams alternatives for European government should treat sovereignty as the primary filter, not a secondary consideration.
For agencies seeking a practical deployment path, secure messaging for European governments and a sovereign Slack alternative for Europe address both the technical and regulatory dimensions.
Self-hosted government chat for mission-critical and defense use cases
Standard government deployments and defense or national security deployments have different requirements. This distinction matters because vendors often conflate them — and agencies selecting a self-hosted government chat solution need to evaluate against the higher standard.
For civilian government agencies handling sensitive but unclassified information, a self-hosted deployment with strong encryption, audit logging, and EU-based infrastructure is typically sufficient. For government messaging apps handling classified communications, the requirements escalate to include hardware security modules, multi-factor authentication with physical tokens, and mandatory air-gap operation.
Military communication introduces additional requirements:
- resilience under degraded network conditions,
- compatibility with tactical radio integration, and
- support for mission-critical communications where message delivery guarantees are operationally significant.
A self-hosted government chat platform that performs well in a corporate environment may fail completely in a contested or austere network environment.
Military messaging systems must also account for coalition interoperability, where partner nations with different security certifications and IT architectures need to communicate securely without compromising each other's networks.
The government chat requirements for day-to-day administrative operations and the requirements for crisis management or combat operations are on the same spectrum. Agencies should deploy their self-hosted government messaging platform to the higher standard and manage permissions downward, rather than deploying to a lower standard and attempting to harden under pressure.
Deployment architecture: a practical comparison
Communication security with a self-hosted government chat: what it actually means
Communication security is not a product feature. It is the sum of architecture decisions, operational practices, and policy enforcement across the entire messaging lifecycle.
A platform with end-to-end encryption provides no communication security benefit if administrators reuse passwords, if endpoint devices are unmanaged, or if users are not trained to recognize social engineering. The platform is a necessary but not sufficient condition. The most secure messaging apps are those that combine strong cryptography with operational security practices enforced at the organizational level.
Government communication infrastructure should be evaluated across three dimensions:
- technical security (encryption, access control, audit),
- legal compliance (data sovereignty, retention, discovery), and
- operational resilience (availability, air-gap capability, failover).
A platform that scores well on two out of three is not acceptable for sensitive government use.
Frequently asked questions about <anything>
self-hosted chat for government
What does self-hosted chat for government mean in practice?
Why do government agencies need a self-hosted chat platform instead of a cloud service?
Which regulations require government agencies to use a self-hosted government messaging platform?
Can a self-hosted government chat platform support multi-agency or coalition communication?
How do agencies evaluate whether a self-hosted government chat solution is suitable for classified communications?
What is the difference between end-to-end encryption and encryption at rest in a self-hosted government messaging context?
How should agencies migrate from a commercial platform to a self-hosted government chat solution?
How should agencies approach the migration from a commercial platform to a self-hosted solution?


- Digital sovereignty
- Federation capabilities
- Scalable and white-labeled


- Highly scalable and secure
- Full patient conversation history
- HIPAA-ready

for mission-critical operations
- On-premise and air-gapped ready
- Full control over sensitive data
- Secure cross-agency collaboration
%201.svg)

- Open source code
- Highly secure and scalable
- Unmatched flexibility


- End-to-end encryption
- Cloud or on-prem deployment
- Supports compliance with HIPAA, GDPR, FINRA, and more


- Supports compliance with HIPAA, GDPR, FINRA, and more
- Highly secure and flexible
- On-prem or cloud deployment



.avif)


